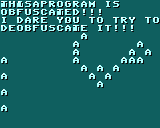

JoBot 2021-12-16 02:57
I dare you to try to deobfuscate it. If you succeed, show me the deobfuscated code, and I shall give you a free library. ^-^ I love challenges.

JoBot 2021-12-16 03:01
If you can make sense of every single detail of the code, you shall be rewarded.
was8bit 2021-12-16 07:17
Decoded.... ;)
was8bit 2021-12-16 07:18
Ceasar cipher, 3 shift, 4 shift... ;)
was8bit 2021-12-16 07:23 (Edited)
I like Vigenère and Playfair... the french Great Cipher is also interesting :)
JoBot 2021-12-16 17:14
@was8bit How difficult was it to deobfuscate?
was8bit 2021-12-16 17:53
Super easy.. i simply used lowes's REPLACE button on the search bar to rename all variables into something more sensible, and the rest was easy... i instantly detected the ceasar cipher code, and even used it in reverse to encrypt my own text ;)
was8bit 2021-12-16 17:59
You may try using a secondary codex to hide the intentions... for example, a string with your made up commands and data, a decoder to break down and interpret your command/data stream, and a router that routes to different subs based on the commands and inputs into the subs the derived data...
Would be tricky trying to split up each "function" into sets of subs that at first glance seem very simple...
In an original lowres program i made a robo drawer that would position and set the pen, and perform different draw commands whic would depend on where the robo was and how the pen was set...
The command string was meant to be readable and therefor editable, but it got no interest...